Malware analysis Malicious activity
4.8
$ 24.50
In stock
(313)
Product Description
Malware Analysis: Protecting Your Network from Cyber Attacks
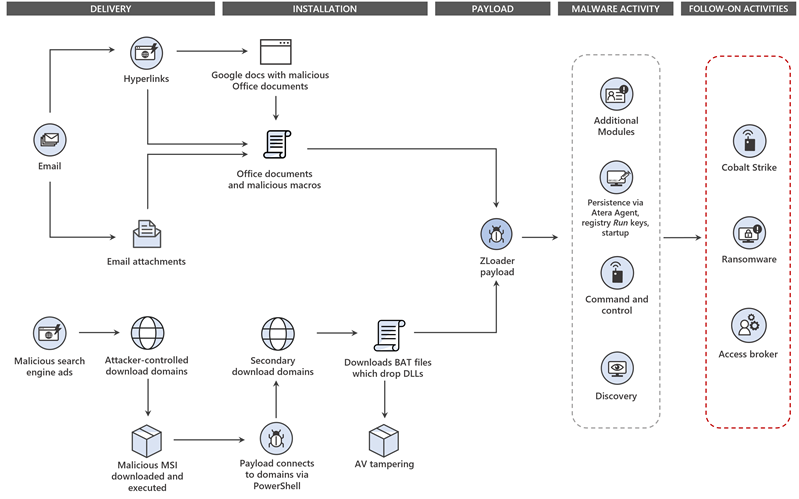
Dismantling ZLoader: How malicious ads led to disabled security

How to Do Malware Analysis?

A Novel Approach to Detect Malware Based on API Call Sequence
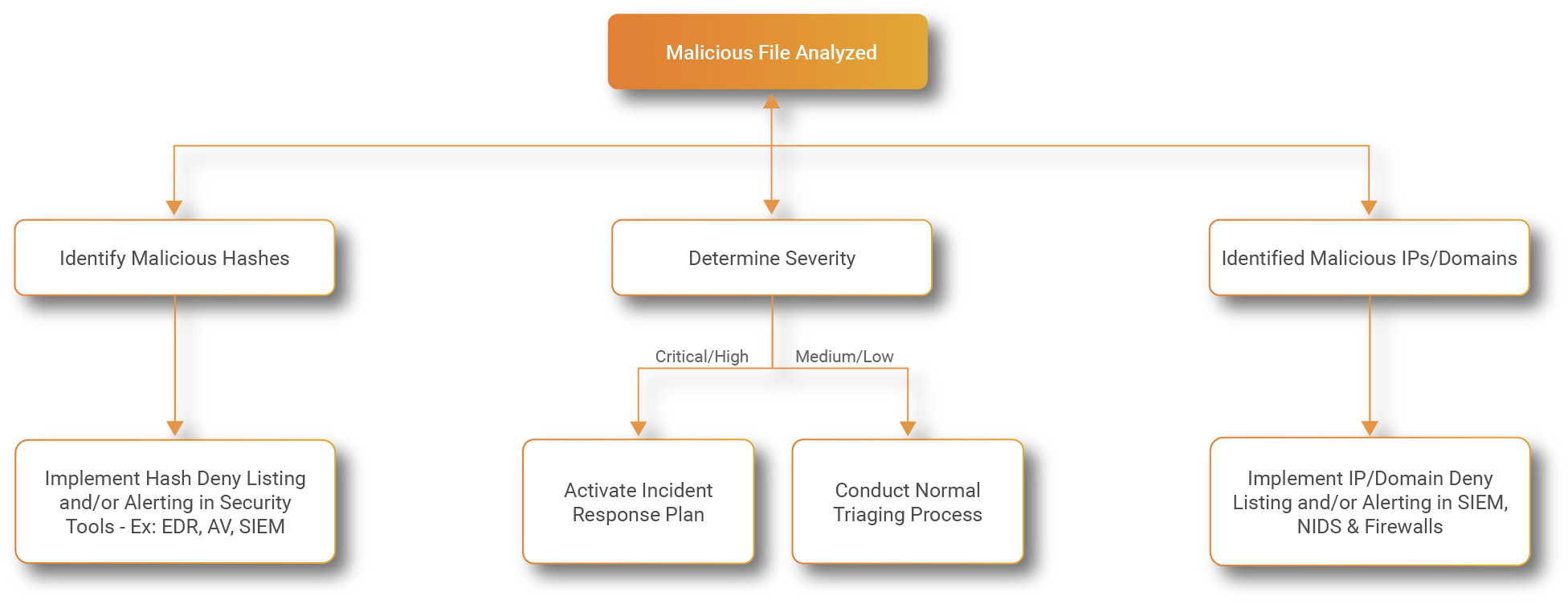
Process flowchart of the malware analysis process during the
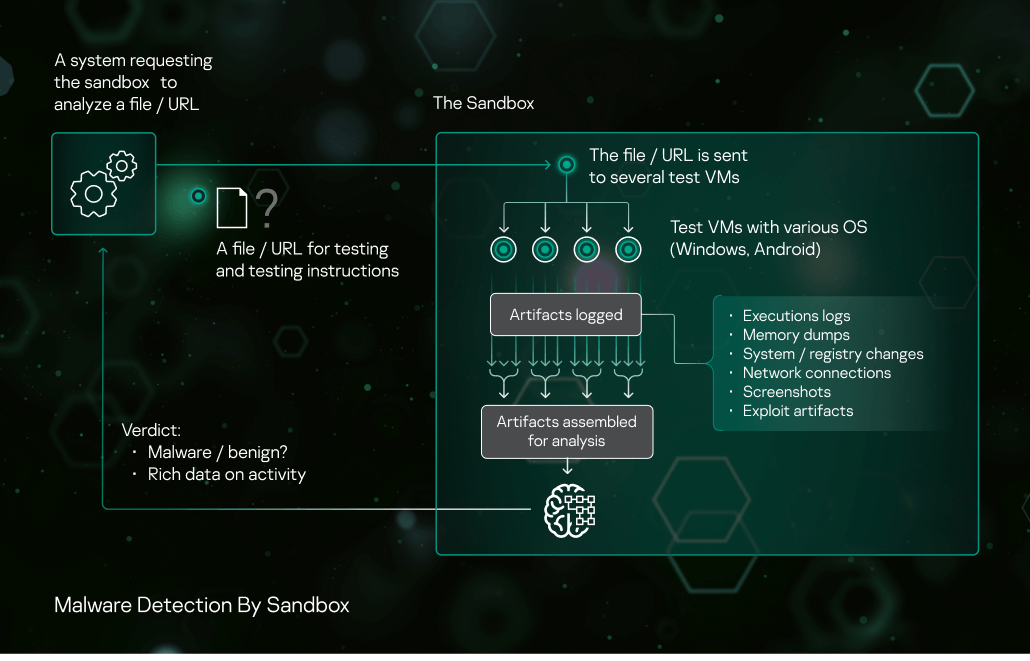
Sandbox Kaspersky

Malware Analysis: Steps & Examples - CrowdStrike

Malware Analysis Solutions - Fast & Accurate Detection - OPSWAT

Intro to malware analysis: Analyzing Python malware

What is Malware Analysis?: Types and Stages Explained









